VPN vs SSH Tunnels

 VPNs Compared to SSH Tunnels
VPNs Compared to SSH Tunnels
People who care about their online security and privacy always reach the same question: What is the difference between a VPN tunnel and an SSH tunnel and which of the two is most secure? Well, there are several differences between the two security methods. SSH was originally created in 1995, and it helped solve the problem of sending data in plain text. When data is sent in plain text, it is very easy for an Internet crook to steal your passwords. At the time, there weren’t many solutions for transferring data in a protected format. In turn, Internet hucksters could capture and read usernames and passwords in plain text since they weren’t encrypted. Typically, SSH tunnels are used when someone wants Internet security without the price tag.
Endpoint Differences
VPNs come in many shapes and sizes, but they are more flexible than SSH tunnels. VPNs can be software based, hardware based, connect an individual to a server, or connect entire networks together over a secure tunnel. SSH tunnels, on the other hand, only encrypt endpoint to endpoint communications. That is to say that SSH tunnels only encrypt a single session between two devices.
The reasons for this is the layer of the OSI model that each security options exists in is different. VPNs operate at layer four (the transport layer) while SSH tunnels operate at layer 5 (the session layer). In addition, both offer the same level of encryption to ensure the security of your data while it is in transit. Neither protocol can currently become cracked or decrypted (although some conspiracy theorists think that the government can break AES-256, there is no proof of this).
Which One is Better?
Many people ask this question, but it’s as easy to answer as the question, “How long is a piece of string?” It really depends on your goals, environment, and needs. VPNs are more versatile, but each have their respective advantages and disadvantages, so let’s take a closer look at each option.
VPNs
One unique benefit of VPNs is that you can cloak or mask your traffic to look exactly like HTTPS traffic from an interceptor’s perspective. This can be a huge benefit under the right circumstances. In addition, you can setup a site-to-site tunnel that encrypts traffic between hundreds – or even thousands – of devices. Furthermore, VPNs can use either TCP or UDP so you can select the best option for your data needs. For example, voice and video streams typically use UDP because it is faster than TCP due to the fact it doesn’t use acknowledgements.
Unfortunately, the VPN industry is very fragmented in terms of standards. There are a variety of VPN security protocols, each with their own individual benefits and nuances. This creates VPN services that all have different support requirements, making them a little harder to troubleshoot.
SSH Tunnels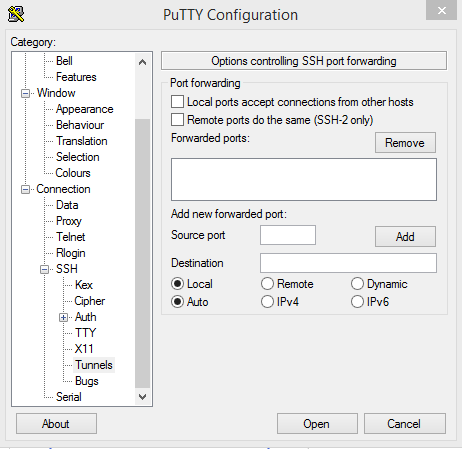
SSH tunnels are fantastic tools to send encrypted data, and they are frequently used in the I.T. world to configure remote devices. Instead of sending configuration commands, usernames, and passwords in plain text, they are encrypted. To implement an SSH tunnel solution, you will need to download and install PuTTY. There are other options, but PuTTY is probably the most popular.
Though SSH is easy to install, it’s hard for non-technical users to setup. Furthermore, an SSH tunnel will only encrypt traffic to certain configured endpoints, which could be advantageous given your web browsing needs. For example, you may not care if a YouTube video you are streaming is intercepted because it would be inconsequential. As such, an SSH tunnel that only encrypts sensitive traffic would mean that your YouTube video doesn’t have increased processing and bandwidth overhead like a VPN connection would.
In summary, we would recommend a VPN tunnel for most users and SSH tunnels to a select few. Though SSH tunnels offer reliable encryption, VPN tunnels are easier to setup and use. In addition, VPN tunnels will ensure that all of your traffic is encrypted without having to configure the nitty gritty details of an SSH tunnel. VPN tunnels are simply more user friendly and deliver fantastic online security.




