Tutorials
Beginners guide to using Tor to browse anonymously
The internet has made our lives easier in many ways, but the price to pay has been high as we have given up our privacy. Social websites like Facebook and Twitter are known for their interest in collecting personal data. While some users share a lot of details about themselves willingly, many popular websites have shady practices that allow them to find out more about their users. Your identity, your location and your browsing habits can be traced by large corporations, your ISP and the government. While some of this information can be used to target you with customized ads and to offer a browsing experience that suits your specific needs, you should always be concerned about other ways in which your data may be exploited.
Cyber criminals can try to access your financial information, steal your identity and take over your online accounts, only to mention a few. Protecting privacy is not only a matter of defending your right to keep some information to yourself, in some cases, it can be crucial in order to protect your own safety. For instance, activists and journalists who seek to expose the brutality of dictatorships, or corruption cases, risk their life if they don’t take the necessary measures to keep their identity protected. Even if you are only using the internet for every day tasks, there is always a chance of being monitored and traced for malicious purposes, which is why, it is important to take the necessary steps to enhance the protection to your privacy. The Onion Router, commonly known as Tor, is one of the ways to browse the internet anonymously and without compromising your privacy.
What is Tor?
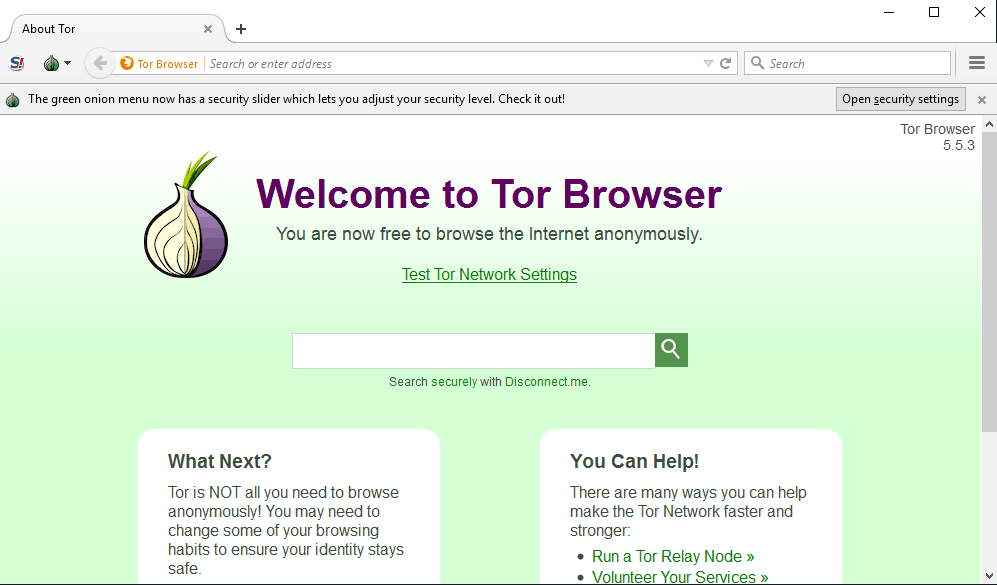
Tor has an interface that resembles popular web browsers like Chrome and Internet Explorer, but it is based on Mozilla Firefox. The configuration has settings specifically designed to suit Tor and enhance privacy. The software is what allows you to access the Tor network, which is the core of Tor’s functionality. It is worth mentioning that a network is a collection of multiple computers that are connected through routers, modems, switches, hubs or other types of devices that allow the computers to interact with each other. The Tor network, also known simply as Tor, is different form other networks and it comprises thousands of relays and bridges.
The relays and bridges are run by volunteers who offer their computers and bandwidth to support Tor’s performance. The way in which Tor works allows people to browse the internet in an anonymous way because their real IP address is hidden. The websites visited via Tor won’t be able to see your true IP address and your online traffic will be protected from those who try to monitor it. Other parties will only be able to see that you are connected to Tor, but they won’t know what websites or services are being accessed.
In addition, Tor offers some hidden services as .onion sites and instant messaging server. The first are websites that are hosted on Tor server and that are hidden by paths that are generated randomly from entry points within the network. Thanks to this, users are able to access the sites, but can’t determine the location of the servers that host them.
How does it work?
Tor manages to support anonymous browsing and offer access to hidden services thanks to the way it is set up. The relays are computers within Tor that are listed in the main directory and they get internet signals from other relays. That signal is then forwarded to the next relay in the route. The route is randomly generated for each connection request or website visited. The relays don’t keep records of these connections, meaning that it is not possible for a relay to report on the traffic that it has dealt with.
Bridges are hidden relays that don’t appear in the main Tor directory. These hidden relays are supported by users who can’t access Tor using the normal setup. This may be due to the fact that the network that they use has a proxy that is blocking Tor traffic. The exit point is the last relay in the path and it is the only part of the network that establishes a connection to the server that you are trying to access. As such, it is the only part that the server can see and it only logs the IP address of that particular relay.
Unless you log into that server using an existing account, that server and its admins, won’t be able to find out your identity. The server simply receives a request from the exit point for the services that it offers and it has to respond to that request. The only thing that it knows is that the information is being sent back to a relay. Apart from that, it has no way of knowing the last destination of the data.
Is Tor fully anonymous?
Tor can keep the data traffic anonymous, but there are some things that you need to keep in mind in order to ensure that your anonymity remains protected. Keep in mind the below:
It is worth noting that since your information is being routed through multiple dedicated relays, your connection will be significantly slower than usual. The speed will be affected by different factors including the speed of the internet connection of the relays used and the amount of traffic they handle. At times Tor may be more congested, which will also have an impact on the speed.
Don’t use Tor to log in to your online accounts and don’t provide any personal information while browsing.
Avoid using websites with heavy traffic or heavy bandwidth
Tor can help you to protect yourself from eavesdroppers, but it is important that you also avoid giving away information that could compromise your identity and privacy. Keep in mind that Tor is not suitable for torrenting, not only because of the slow performance, but also because the network is run by volunteers. Torrenting could land someone in trouble and it would be a shame that a project that aims to help people to defeat censorship and share information securely and anonymously, could lose volunteers and be affected just because some people are misusing the network. If you want to use torrent services anonymously, the best option is to get a VPN.




