How to Install OpenVPN Server on Ubuntu Version 8 (Jessie)

Linux is wonderful due to its stability and the fact that it is completely free. The only issue people seem to have with Linux, though, is that there seems to be a limitless number of flavors – or distributions – of this operating system. There are some differences between the structures of different Linux distributions, and as such, VPN server configuration steps change from one variety of Linux to another. However, for this demonstration, we will be using the latest version of Debian to install and configure OpenVPN server.
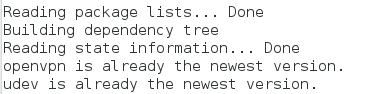
To start off, we are going to want to update and upgrade your current system with the following commands:
- apt-get update
- apt-get upgrade
- apt-get dist-upgrade
Now download and install OpenVPN.
- apt-get install openvpn
Now it is time to setup easy-rsa. Start by copying the following file and entering the following commands:
- cp -prv /usr/share/doc/openvpn/examples/easy-rsa/2.0 /root/easy-rsa
- cd /root/easy-rsa
- cp vars{,.orig}
Next, you will want to edit the following file in your favorite text editor. Replace the fields that are enclosed by quotes as they apply to you:
- vim ./vars– KEY_SIZE=2048
- KEY_COUNTRY=”US”
- KEY_PROVINCE=”MO”
- KEY_CITY=”Kansas City”
- KEY_ORG=”organization”
- KEY_EMAIL=”me@example.com”
Next, we will export the keys, delete any previously created keys, and build the CA as follows:
- source ./vars
- ./clean-all
- ./build-ca
Simply run the following command to build the certificate, and input a ‘y’ for the following two prompts.
- ./build-key-server ca-name
Now you need to build the Diffie-Hellman (DH) certificate as follows:
- ./build-dh
To build the client certificate and generate the HMAC (Hash-based Message Authentication Code) with the following commands. After you run the first command, simply enter a ‘y’ to both prompts before proceeding with the next commands.
- ./build-key key-name
- openvpn –genkey –secret /root/easy-rsa/keys/ta.key
You will also want to copy the certificates and keys in an ‘etc’ directory with the next two commands:
- mkdir -p /etc/openvpn/certs
- cp -pv /root/easy-rsa/keys/{ca.{crt,key},ca-name.{crt,key},ta.key,dh2048.pem} /etc/openvpn/certs/
Also, run the next command to make sure your server file is as follows:
- cat > /etc/openvpn/server.conf
Currently, it should look like this:
- cat > /etc/openvpn/server.conf
- port 1194
- proto udp
- dev tun
- ca /etc/openvpn/certs/ca.crt
- cert /etc/openvpn/certs/neutron.crt
- key /etc/openvpn/certs/neutron.key
- dh /etc/openvpn/certs/dh2048.pem
- tls-auth /etc/openvpn/certs/ta.key 0
- server 192.168.88.0 255.255.255.0
- ifconfig-pool-persist ipp.txt
- push “redirect-gateway def1 bypass-dhcp”
- push “dhcp-option DNS 8.8.8.8”

- push “dhcp-option DNS 8.8.4.4”
- client-to-client
- keepalive 1800 4000
- cipher DES-EDE3-CBC # Triple-DES
- comp-lzo– max-clients 10
- user nobody
- group nogroup
- persist-key
- persist-tun
- #log openvpn.log
- #status openvpn-status.log
- verb 5
- mute 20
Next, we will want to do two things. Firstly, we will want to restart the VPN service with all of the changes we have made. Secondly, we will want to start the server automatically when the system starts up.
- service openvpn restart
- update-rc.d -f openvpn defaults
Now open the following file and either uncomment or add the following code to enable traffic forwarding.
- vim /etc/sysctl.conf
- :%s/net.ipv4.ip_forward = 0/net.ipv4.ip_forward = 1/
- sysctl -p
Don’t forget to configure IPTables as follows:
- iptables -A INPUT -p udp -m state –state NEW -m udp –dport 1194 -j ACCEPT
- iptables -A FORWARD -s 192.168.88.0/24 -j ACCEPT
- iptables -A FORWARD -m state –state RELATED,ESTABLISHED -j ACCEPT
- iptables -t nat -A POSTROUTING -s 192.168.88.0/24 -o eth0 -j MASQUERADE
- # in openvz/vservers you may need the following instead
- # iptables -t nat -A POSTROUTING -s 192.168.88.0/24 -j SNAT –to-source <PUBLIC_VPN_IP>
- iptables-save > /etc/iptables.rules
In this example, 192.168.88.0/24 is your local subnet. You can substitute a value that’s appropriate for your local network. Lastly, you will also need to install the VPN client on any device you want to connect to your VPN server. Be sure to create the client configuration file as follows:
- cat > /etc/openvpn/client.conf
- client
- remote <PUBLIC_VPN_IP>
- ca /home/d/confs/certs/vpn/ca.crt
- cert /home/d/confs/certs/vpn/blackhole.crt
- key /home/d/confs/certs/vpn/blackhole.key
- cipher DES-EDE3-CBC
- comp-lzo yes
- dev tun
- proto udp
- tls-auth /home/d/confs/certs/vpn/ta.key 1
- nobind
- auth-nocache
- script-security 2
- persist-key
- persist-tun
- user nobody
- group nogroup
Finally, you will need to install the VPN client on any devices that you want to connect to your OpenVPN server. Please understand that you will need to copy the files for the keys and certificates to connecting devices as well. At the end of this process, your VPN server will be ready to accept incoming client connections – as long as it is powered on.





I was so excited to try this but then there is misssing files already
“cp -prv /usr/share/doc/openvpn/examples/easy-rsa/2.0 /root/easy-rsa”
there is no easy-rsa on examples directoty and now what?